Oh No! this Data is Encrypted it is hard to Crack and it can Take alot of time.
Encryption is a great way to protect your data from hackers. If you use Facebook, Gmail or other online services, you have probably already used encryption. But you might not know exactly what encryption is, how it works, or why hackers hate it. Here's everything you need to know about encryption.
What Encryption Means?
Encryption is a way of scrambling data so that only authorized parties can understand the information. In technical terms, it is the process of converting human-readable plaintext to incomprehensible text, also Known as ciphertext. In simpler terms, encryption takes readable data and alters it so that it appears random. Encryption requires the use of acryptographic key: a set of mathematical valuthat both the sender and the recipient of an encrypted message agree on.
How Does it Work?
Encryption uses an algorithm to scramble, or encrypt, data and then uses a key for the receiving party to unscramble, or decrypt, the information. The message contained in an encrypted message is referred to as plaintext. In its encrypted, unreadable form it is referred to as Ciphertext.
Types of Encryption Methods:
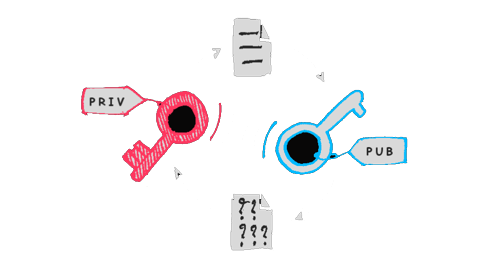
There are two types of cryptographic key systems, symmetric and asymmetric.
With a Symmetric key system (also known as secret key system), all parties have the same key. The keys can be used to encrypt and decrypt messages and must be kept secret or the security is compromised. For the parties to get the same key, there must be a way to securely distribute the keys. While this can be done, the security controls needed can make this system impractical for widespread and commercial use on an open network like the Internet. Asymmetric key systems can solve this problem.
In an Asymmetric key system (also known as a public/private key system), two keys are used. One key is kept secret, and therefore is referred to as the "private key." The other key is made widely available to anyone that needs it and is referred to as the "public key." The private and public keys are mathematically related so that information encrypted with the public key can only be decrypted by the corresponding private key.
Although all these algorithms involve substituting one thing for another (e.g., taking a piece of plaintext and then substituting the appropriate ciphertext to create the encrypted message), Symmetric Encryption Algorithm uses the same cryptographic key for encrypting and decrypting information, whereas the Asymmetric Encryption Algorithm uses a private key and a public key for Encryption and Decryption.
What is Encryption Algorithm and it's Types:
An encryption algorithm is the method used to transform data into ciphertext. An algorithm will use the encryption key in order to alter the data in a predictable way, so that even though the encrypted data will appear random, it can be turned back into plaintext by using the decryption key.
Most Comman Encryption Algorithms are:
• Advanced Encryption Standard (AES Algorithm)
• Triple Data Encryption Algorithm (3 DES Algorithm)
• SNOW Algorithm
• Rivest-Shamir-Adleman Algorithm (RSA Algorithm)
• Elliptic Curve Cryptography (ECC Algorithm)
The Decryption of Text from the content page is:
ZVdQB2pSr1HtY3LwMq7gmZQG6VXZeEqj
73kjZY10zIs=
-> Welcome to Virtual Developers