Wait! My Account is showing their is Some Suspicious Activity and my device might be Hacked!!
Have you ever thought about the security precautions you take to protect your devices from hackers? If you’re like most people, you probably have antivirus software and a firewall. But few people realize their phones and computers are also vulnerable from another source that is much more common: and it can get hacked by their very own actions.
Let's See What are the things that you Accidentlty do that helps hackers to get into your Devices.
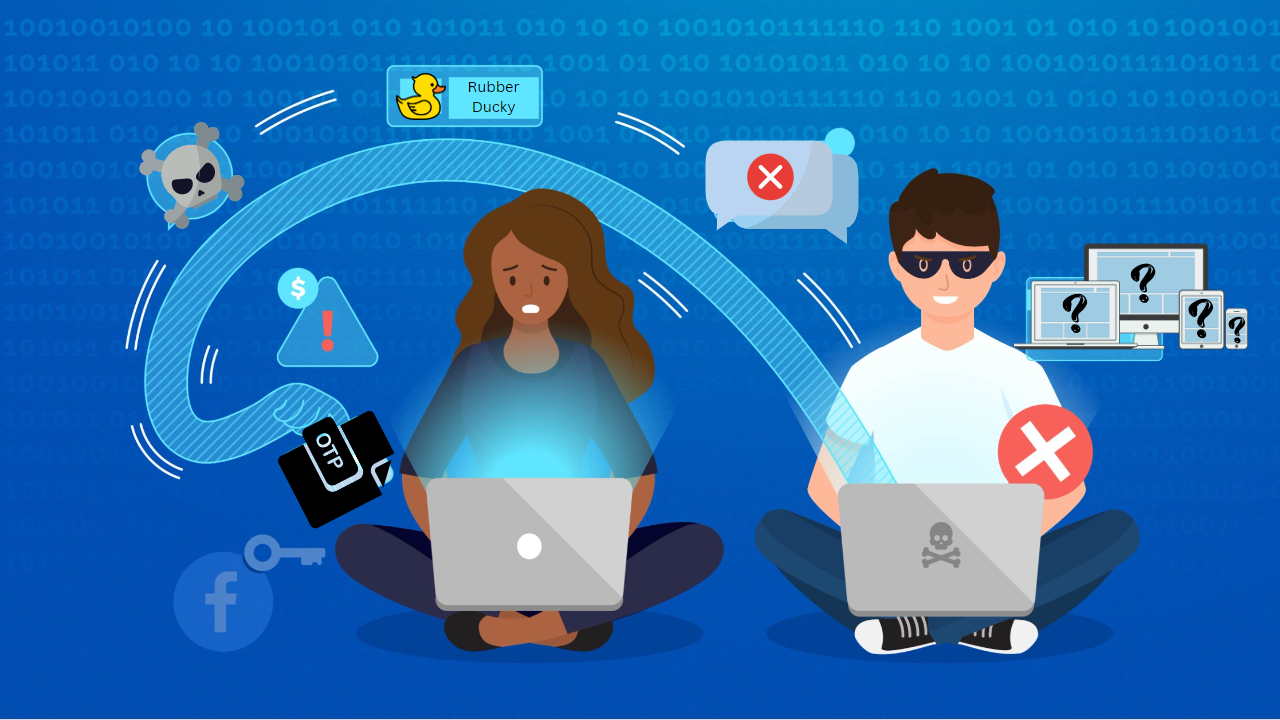
Ever Wonder how Hacker gained your device access?
The only way they gain access to your Device or accounts that easily is through your Permission, but you think that you never permitted them then how?
Well, you never permitted them directly but you did Indirectly through links (This method is known as Phishing) or thinking the person is genuine and sharing some of your details with them (This method is known as Spoofing).
Ways through they can gain access to your Devices :
The things through Which a hacker can access your device or account are:
• OTP's
• Links (Through Sending Sms or Emails)
• Rubber Ducky attack
• Virus
• Unknow Devices
Let's See how the things mentioned above help the hackers to gain access:
OTP's :
Yes, you saw the correct thing OTPs play a very vital role in security nowadays and sharing them with someone is the dumbest thing you can do.
Remember one thing you can get calls from any person asking for the OTP saying we are calling on the behalf of this (bank, etc.) which is Nothing more than a Scam because if they are calling from some Professional Validate Structure then they never need your Details or anything to validate you.
Links :
You got a Message or Mail having a link to some Website saying you won a lottery or through this, you can get a chance to win a lottery or don't know what, This is nothing but a way to attract the person to click the bait which is set up for them and make them lose everything we have.
This bait redirects you to random sites but in the background the things that a hacker needs to access your device or account they got them (IP address, location, Personal Details, etc.) So never click on unknown links if you want that only you use your device or account.
Rubber Ducky attack :
The Most lethal Device used by hackers is The rubber ducky which looks like a simple Pendrive but has a code embedded in it that steals your data in the background and stores it secretly so that the hacker can access it later and gain your device or accounts authority. So it's better if you think before using an unknown user Pendrive because it can be a rubber ducky in disguise.
Virus :
Yes, an Infected Device can share a lot of your data with someone more anonymous than you think, having an infected device means your security is ZERO which can lead to key Spoffing, spying, or many other things. The best example of this can be a Trojan Virus which looks like a simple software or app but there is a malicious code hidden inside it waiting for the right moment to activate and steal everything. So it's better if you keep your system clean and secure.
Unknown Devices :
Unknown devices can be suspicious attackers who can kill you with a sweet knife. Did You know that an unknown device can harm you ina way that you can't even recover from the loss? Well, the answer to this is YES. The unknown device can have those things that can make you do things you don't want to do and can ransom you for your Security.